National Cyber Security Awareness Month 2020

NCSAM 2020 at UC – Going Virtually Viral!
October is National Cyber Security Awareness Month. UC events are completely online this year and we have something for everyone: cinema events; a Cyber Escape Room; comedic Security Improv, Security expert discussions highlighting topics such as industry trends, keeping our children safe online, and more; teambuilding competitive games like Security Feud; prizes, giveaways, and so much more!! If every person tells two others, and they tell two people, and they tell two people, before long, we can take NCSAM at UC virtually viral! #BeCyberSmart and spread the word!
We've created NCSAM 2020 Zoom backgrounds for every location. Download yours today!
Visit UC location websites to learn more about their Information Security programs.
UC Agriculture and Natural Resources; UC Berkeley; UC Davis; UC Davis Health; UC Irvine; UC Irvine Health; UC Los Angeles; UC Los Angeles Health; UC Merced; UC Riverside; UC Riverside-School of Medicine; UC San Diego; UC San Diego Health; UC San Francisco; UC Santa Barbara; UC Santa Cruz;
See our full calendar of events below and register to join.
NCSAM UC-Systemwide Events:
|
Beginning October 1, 2020 On Demand |
True Eye - Cinema EventTrue Eye is a thriller which follows new-hire, Adrian Bridges, through his first day at a global AI-technology firm. Adrian’s policy orientation and security training quickly spin into suspense and intrigue as his personal AI device, Guide, starts asking him to do unethical and even dangerous things with sensitive data. His adventure offers a glimpse into proper operational security, how technology affects people and what we can do about it. Trailer |
|
October 1, 2020
10 AM - 11 AM
|
Electronic Records Management - Now, More Than Ever(Hosted by UC Records Management Committee)
Celebrate Electronics Management Day by joining this event as Panelists including experts in Archives, Records Management, Privacy and Information Security discuss managing electronic records. With audience Q&A afterward. Speakers include: Marlayna Christensen - With the UCs since 1999 and the University Archivist at UC San Diego since 2016. As University Archivist, she coordinates with offices and organizations across the campus to collect analog and digital records documenting the achievements, challenges, events, and people at UC San Diego, ranging from top administrators to student organizations. Kelley Walker - Information Practices Coordinator and Campus Records Manager, UC Davis Office of the Campus Counsel and concurrently serves as Interim Chief Administrative Officer for the Vice Chancellor’s Office of Diversity, Equity and Inclusion since September 2019. Carolyn Tuft - Assistant Director for Business Intelligence, UCSF Real Estate. She promotes good information governance practices to better manage one of UCSF’s most valuable assets, information. Prior to this role, she was the Senior Digital Project Manager. As a PM, she facilitated moving to paper lite work processes in preparation for moving to open plan workspaces. Laurie Sletten - UCOP Records Manager. She convenes the UC Records Management Committee, which by policy coordinates the ongoing systemwide development and management of policies and procedures that promote sound, efficient, and economical records management in alignment with current laws and industry best practices for the university. Pegah K. Parsi - Campus Privacy Officer for UCSD where she manages a portfolio of privacy initiatives related to employees, students, applicants, alumni, and research participants. David Rusting - Systemwide Chief Information Security Officer at the University of California, Office of the President, where he leads the collaboration, development, and implementation of information security strategy and initiatives across the UC system. |
|
October 5, 2020
Noon - 1 PM
|
Hate Passwords? You're Not Alone: Why We Still Have Passwords in 2020(Hosted by UCSB) There are few things in the world more ubiquitously despised than passwords. How many times have you tried to login to a website, only to realize that you “forgot your password,” or tried to create a new password only to have every attempt rejected because it is not secure enough? And then, after satisfying all of these requirements, you get a text with a “security code” that you have to type in -- not ideal. How did we get ourselves in this situation, and does any of this even help from a security point-of-view? In this talk, I will present a brief history of passwords and discuss the evolution of authentication. Then, I will dive into the details of real-world attacks against passwords, and provide insights as where the various security measures (e.g., strict passwords requirements and text messages) do and do not help. My goal is to pull the curtain back on the various forms of password-based authentication and let you be the judge if you should be frustrated with or grateful for the various “security” hops that you must jump through on a daily basis. |
|
October 6, 2020
10 AM
|
Q & A with John Pescatore, Director of Emerging Threats, SANS Institute(Hosted by UCSF)
During this session SANS’ John Pescatore will highlight the top 3 security issues hitting organizations in 2020/2021 followed by Ken Newton, UCSF IT Security Operations Manager asking questions to drill down in areas of particular interest to the USCF community, then selected questions from the audience. John Pescatore joined SANS in January 2013 with 35 years of experience in computer, network and information security. He was Gartner’s Lead Security Analyst for 13 years, working with global 5000 corporations and major technology and service providers. Prior to joining Gartner Inc. in 1999, Pescatore was Senior Consultant for Entrust Technologies and Trusted Information Systems. Prior to that, Pescatore spent 11 years with GTE developing secure computing systems. Pescatore began his career at the National Security Agency, where he designed secure voice systems and at the United States Secret Service, where he developed secure communications and surveillance systems. He holds a BSEE from the University of Connecticut and is an NSA Certified Cryptologic Engineer. |
|
October 7, 2020
10 AM - 11 AM
|
Using Zoom Security & Awesome New Features(Hosted by UCSB) |
|
October 7, 2020
1 PM
|
FireEye Presents - Cybersecurity & Safety for Families
Ric Messier, CCSP, GCIH, GSEC, CEH, and CISSP, Author, Educator, Senior Security Consultant at FireEye Mandiant The fully-connected, digital world has made it a lot easier for the bad guys to attack us in ways we have never had to deal with before. It’s not just e-mail anymore. It’s Snapchat and Facebook and Twitter and text messages and so many other communications avenues. It’s important for all families to understand how criminals are trying to get at them through these pathways that have allowed for unprecedented levels of communication between humans around the world. This presentation will cover the following topics:
|
|
October 8, 2020
2 PM
|
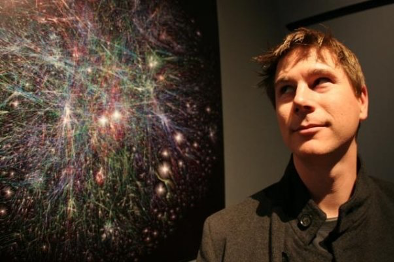
Barrett Lyon Presents: Understanding Security Through Visualization of the Metaphysical(Hosted by UCSF)
When it comes to security practitioners, there are different learners - visual and contextual. Traditionally in security, users interact with the network architecture in a non-visual way. But for security practitioners that learn by seeing, it becomes difficult to really understand what is happening on their networks. Realizing this, technologists are slowly shifting to create interfaces and data in visually useful forms, leveraging art in ways that give visual learners the ability to do their job better. The internet - the largest network of all - is abstract and hard to visualize, but it has been made more visually approachable by the Opte Project, an open-source initiative to create a visual representation of the metaphysical spaces of the internet. Created by Barrett Lyon, who is the former founder and CTO of Prolexic Technologies, the first managed service to defend enterprises from DDoS attacks (acquired by Akamai), the former founder and CTO of Defense.Net (acquired by F5 Network) and the former Co-founder and CTO of BitGravity (acquired by Tata Communications), Opte visually showcases how each connection works, and its influence along with the rise and fall of networks and even countries over time. As CEO and co-founder of Netography, a security platform, Barrett and his team are applying the same approach to security, by creating interfaces that connect and visualize data in meaningful ways. In an era of COVID-19, when security teams are spending more time interfacing with tools, and less with each other, visual learners must have better tools to see the whole picture, in order to protect their networks. |
|
October 9, 2020
9 AM - 10 AM
|
Box Security & Usability Tips(Hosted by UCSB) |
|
October 12, 2020
Noon - 1 PM
|
How "Smart" are Smartcards? A Hacker Perspective on Those Plastic Cards(Hosted by UCSB) |
|
October 14, 2020
TBD
|
UC Fall 2020 Cyber Security Summit
The Fall UC Cyber Security Summit will be held online on October 14th. We are excited about sharing our collective expertise in order to better safeguard UC’s mission of teaching, research, and public service. |
|
October 15, 2020
1 PM
|
FireEye Presents - Election Safety with Jon Ford, Mandiant, Cybersecurity Expert, and Professor.
Cyber criminals and bad actors can create chaos in state and local voting and election systems. Mandiant provides election security to over 100 jurisdictions across the United States to better prepare against election security threats. To develop solutions and security programs to counter cyber threats to elections, government agencies have leaned on industry experts with frontline experience to protect our democratic elections. Jon Ford has more than 22 years of cybersecurity experience supporting commercial, federal and state, local, and education clients. |
|
October 15, 2020
1 PM
|
Darktrace Presents - Securing the New Normal: How Cyber AI Learns on the Job(Hosted by UCSB)
The future of work remains unpredictable and uncertain. More than ever before, business leaders need to remain confident that their operations can continue securely in the face of global or even regional crises, and while sections of the economy are slowly re-opening, cyber-attackers are ramping up their campaigns. As businesses look set to rely on cloud and SaaS tools for the long term, our digital environments are going to be more dynamic than ever. Yet organizations are finding themselves undergoing a delicate balancing act—each new work practice and technology that is introduced also brings unforeseen risk. Static, legacy approaches have become redundant, both unintelligent and ill-equipped to adapt. Organizations must rethink their approach to security ,and rely on new technologies like AI to achieve much-needed adaptability and resilience. Darktrace is the world leader in cyber AI technology, and leverages unsupervised machine learning to seamlessly adapt and integrate into changing environments, and to detect and respond to attacks in the earliest moments. In the face of an uncertain present and future, Cyber AI enables businesses to continue communicating, operating, and innovating. |
|
October 16, 2020
1 PM
|
Hacker Stories with Chris Hadnagy
Chris specializes in understanding how malicious attackers exploit human communication and trust to obtain access to information and resources through manipulation and deceit. His goal is to secure companies by educating them on the methods used by attackers, identifying vulnerabilities, and mitigating issues through appropriate levels of awareness and security. |
|
October 16, 2020
1 PM
|
Doing Our Part to Stay Cyber-Safe with Joseph Oregon, Cybersecurity Advisor, Dept of Homeland Security(Hosted by UCI)
As we adjust our personal, professional and educational lives around COVID-19, we need to be mindful about the threats that still lurk online. Join us and our guest Mr. Joseph Oregon from the Department of Homeland Security’s newly created agency to address cyber and physical risk, the Cyber Security Advisor for the Cybersecurity and Infrastructure Security Agency (CISA) as we discuss how to do our Part to stay cyber-safe. |
|
Beginning
October 19, 2020
|
Cyber Escape Room Online |
|
October 19, 2020
Noon - 1 PM
|
What is Hacking, Really? Insights into Breaches and Exploits(Hosted by UCSB)
“Hackers” have become emblazoned in our society. They dominate news headlines, are featured in prominent Hollywood movies, and have become larger than life -- instilling fear in IT professionals and awe in many young computer scientists. Who are these people, what does it mean “hack” something, and what the heck is a binary? Surely, you have seen a news headline that talks about hackers stealing data, taking over cars, or disrupting power plants and thought to yourself, “how did they do that; is that even possible?” In this talk, my goal is to convince you that “hacking” isn't that hard, and try to tease apart fact from fiction with respect to hackers. I will highlight some hacking techniques and show you how to “own” a computer. We will explore some of the technical limitations of our current computing systems and why they are exploitable. Finally, I will walk you through a simple example of binary exploitation, and how you can make a program do things it wasn't intended to do. At the end of this talk, you should be able to read news headlines with sufficient skepticism and, in some rare cases, considerable respect for the hacker’s skills. |
|
October 20, 2020
Noon - 1 PM
|
Women in Cybersecurity - A Panel Discussion(Hosted by UC Merced) This year, the highlight of the NCSAM at UC Merced will be our "Women in Cybersecurity" panel moderated by AVC and CIO, Ann Kovalchick. Panelists will give their unique perspectives on the triumphs and challenges women face in the world of cybersecurity. The discussion will be followed by a Q&A session to answer your questions. Register as soon as possible to attend! Panelists: Moderator: |
|
October 20, 2020
1 PM
|
FireEye Presents - Elevate: Cybersecurity & Diversity in the C-Suite and the Boardroom.
Alexa King, Executive Vice President and General Counsel at FireEye Although diversity in the c-suite and the boardroom is improving, there is more work to be done. Alexa will discuss opportunities that exist for women in cybersecurity, diversity in the boardroom and the importance of mentorship. |
|
October 21, 2020
10 AM
|
Keeping Children Safe Online
Join us for Living Security's Live Webinar diving into keeping children safe online. Mark your calendars and register to attend this informative event. |
|
October 22, 2020
2 PM
|
Cyber Threatscape with FBI Special Agent, Michael Sohn(Hosted by UCI)
Understanding what the cyber threats are to UCI Faculty and Students. The FBI will share its perspectives on the cyber threat landscape, and will provide tips to protect for protecting ourselves fom them. |
|
October 22, 2020
4 PM - 5 PM
|
The State of Authentication with Chad Spensky, Founder & CEO - Allthenticate(Hosted by UCSB). |
|
October 23, 2020
9 AM - 10 AM
|
Box Security & Usability Tips(Hosted by UCSB) |
|
October 23, 2020
10 AM - 11 AM
|
Department of Homeland Security - Cybersecurity & Infrastructure Security Agency (CISA) Presents:Current Trends in K-12 and Higher Education Cybersecurity Issues and Risk Mitigation(Hosted by UCSF) Joseph Oregon serves as the Cybersecurity Advisor, Region IX, for the Cybersecurity Division (CSD), Cybersecurity and Infrastructure Security Agency (CISA). He supports the Department of Homeland Security (DHS) mission of strengthening the security and resilience of the nation's critical infrastructure. His program coordinates cyber preparedness, risk mitigation, and incident response, and provides cyber security resources, including assessments, to the nation’s sixteen critical infrastructure sectors and state, local, tribal, and territorial government entities. |
|
October 23, 2020
1 PM
|
Fish Sticks Comedy - Security Improv
Fish Sticks Comedy is one of the largest, always all-age appropriate improv comedy teams in the US... Their mission — to bring people closer to each other and their communities through comedy improv. They will make our cheeks hurt from laughing, and do more than entertain. They will create a UC community experience through their unique Cybersecurity Improv! Please join us. |
|
October 26, 2020
Noon - 1 PM
|
Are My (Internet of) Things Vulnerable? A Look at the Security of Embedded Systems(Hosted by UCSB) |
|
October 28, 2020
10 AM - 11 AM
|
Zoom Security & Cool New Features(Hosted by UCSB) |