Connect Securely: 2018 National Cyber Security Awareness Month Toolkit
Materials in this toolkit are available to the entire UC community.
For editable files beyond what is available here, please contact your Systemwide Information Security Awareness Workgroup rep(s), listed to the left. If your location isn't listed, please email Cecelia Finney at cecelia.finney@ucop.edu.
Posters:
Click on thumbnail for full size flyer.
|
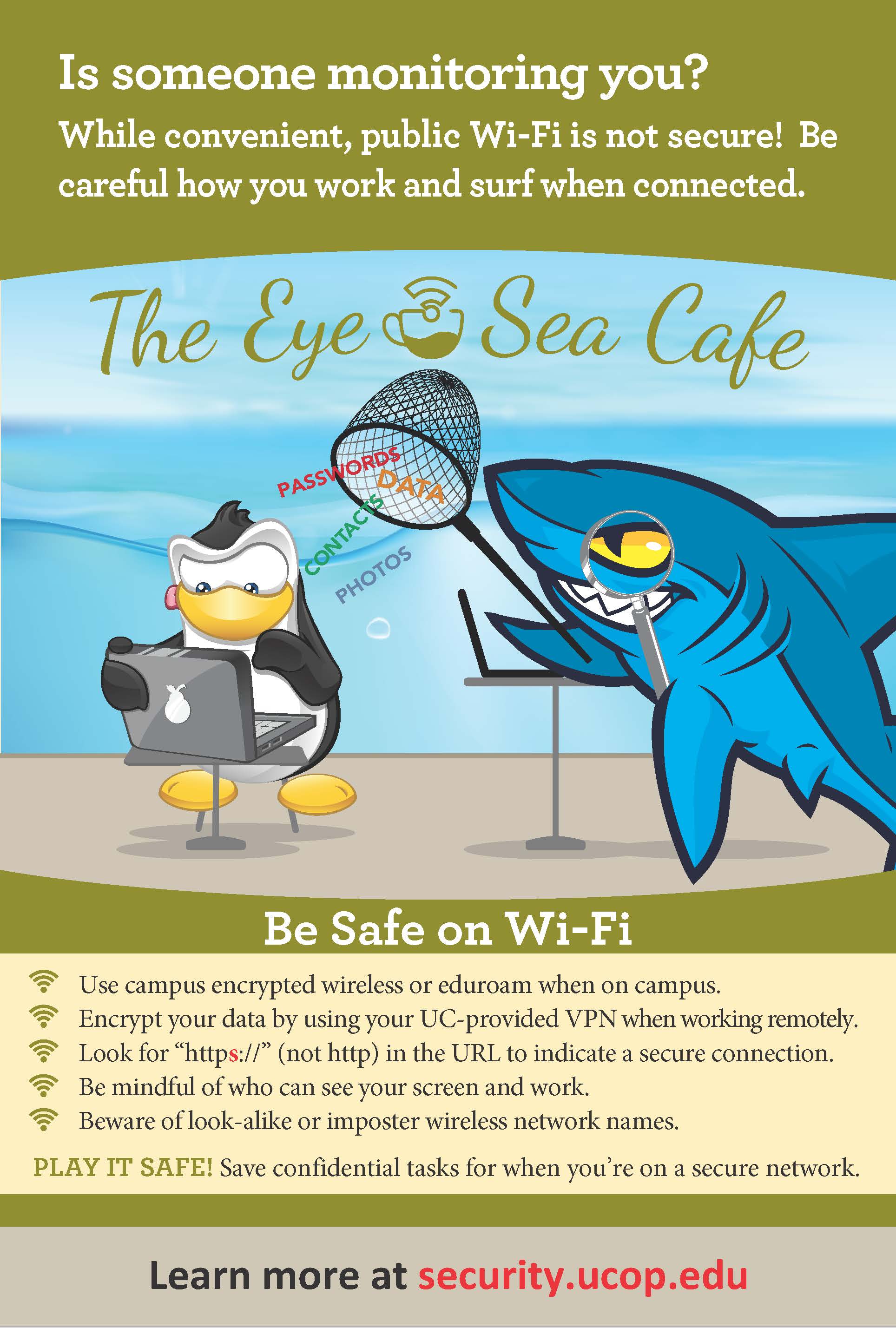
Be Safe on Wi-Fi |
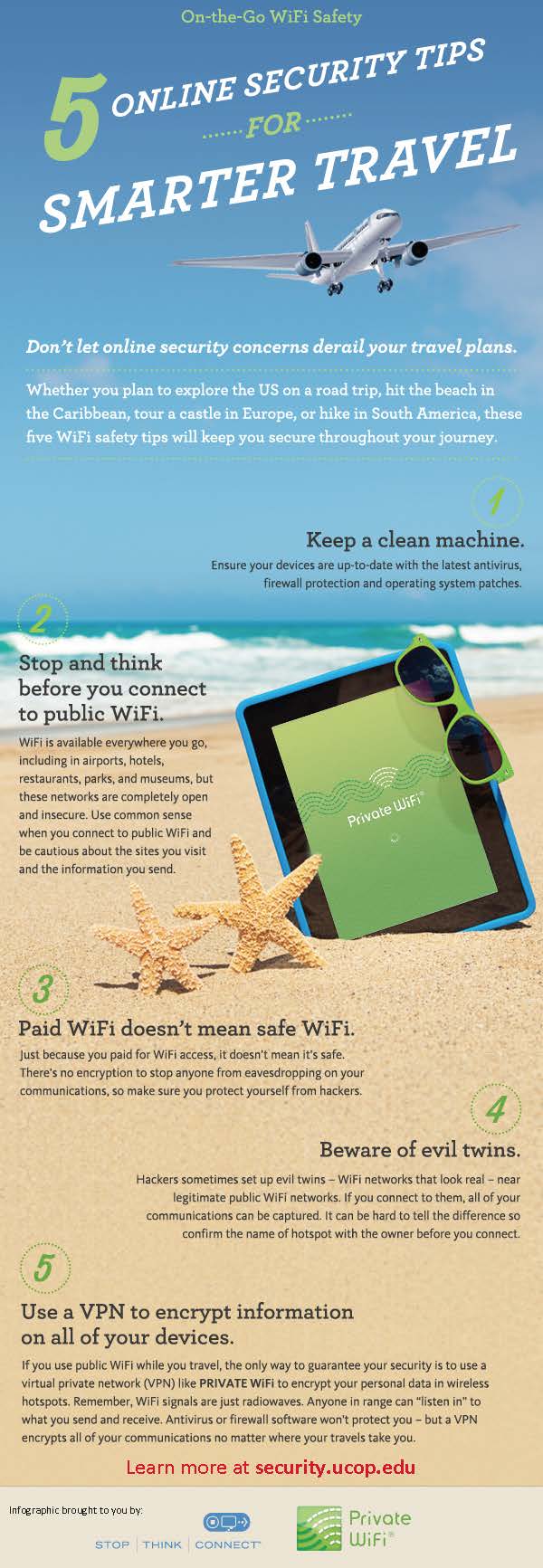
Wi-Fi Security Tips |
Video short:
"Be Safe on Wi-Fi" - Created by UCSB. Mirrors the tips on the penguin/shark poster.
https://www.youtube.com/watch?v=efjl-c6XidE (0:50 sec)
FAQ for Connecting to the Internet Securely:
- How do I connect securely when I’m on campus?
- If you have the option, connect to a wired port on campus. If you have to use wireless, make sure you are connected to your campus’ encrypted wireless network or to eduroam, which is also secure and encrypted.
- Contact your IT department if you’re not sure of the exact name of the encrypted wireless network you should use on campus. Look-alike imposter networks can harm your device and sometimes even see everything you’re doing online, so always ask if you’re not positive.
- How do I connect securely when I’m off campus?
- If you must use a public network, use a virtual private network (VPN) if you have one. This will encrypt your connection to provide a basic level of security. Please see question #4 for more information about VPNs.
- Confirm websites are encrypted by making sure that the URL starts with https, not http. The “s” stands for “secure”.
- Many universities worldwide have eduroam, not just UC. Eduroam is secure and encrypted, so if you’re ever visiting another campus, check for eduroam before connecting to the guest or public wireless.
- If your device has a cellular data plan, using your cellular data is generally more secure than using a public wireless network. Similarly, your own mobile network connection, also known as your wireless hotspot, is generally more secure than using a public wireless network. Use these features if they’re included in your mobile plan.
- What actions can I take to be less vulnerable/less prone to attacks when I’m online?
- Make sure all your devices are up-to-date with the most current patches/updates. Enable automated software updates whenever possible, and restart your devices periodically. Having the latest updates is one of the best defenses against viruses, malware, and other online threats. If any of your devices are managed for you, contact your IT department to see if there is anything you should do to make your device safer.
- Choose passwords that are long and strong, use different passwords for different accounts, and never share your passwords.
- Disable auto-connect features and always log out. This prevents your devices from automatically connecting to unknown networks that may have malicious intentions.
- Don’t click on unknown links or download unknown files or apps. These can harm your devices and put your information at risk.
- Don’t do anything on a public/shared computer or device (e.g., library computers, kiosks, borrowed devices) that requires you to log in or send sensitive information.
- Similarly, avoid doing anything sensitive over public networks. Examples include online shopping, banking, medical, sending forms or documents with personal information, etc.
- What is a VPN and when should I use it?
- “VPN” stands for “virtual private network”. A virtual private network protects your data by creating an encrypted connection between your device and a VPN server. It will also mask your identity because your transmissions appear to come from the VPN server, instead of having a direct link to your computer.
- Use a VPN when you connect to Public Wi-Fi or public Internet to secure your data and connections.
- See if your campus provides a VPN that you can use. Your IT Department may also have VPN recommendations for your personal use.